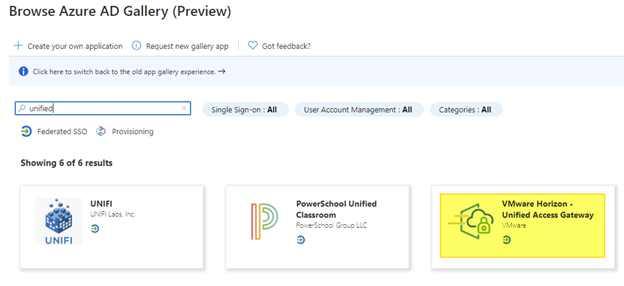
Configure a enterprise application on Azure AD, configure it and export XML
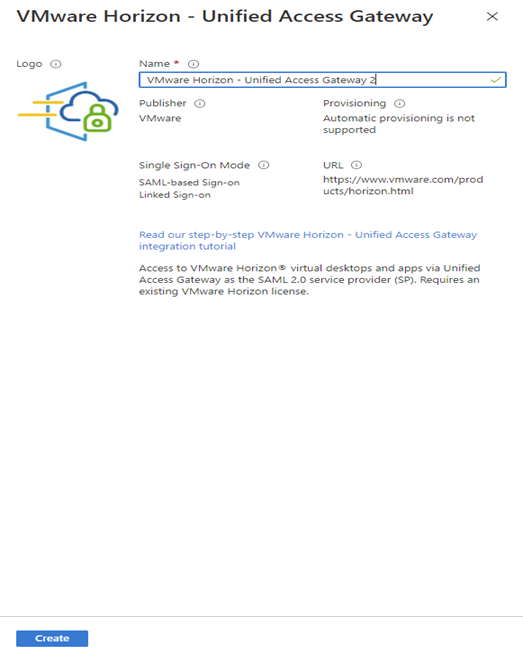
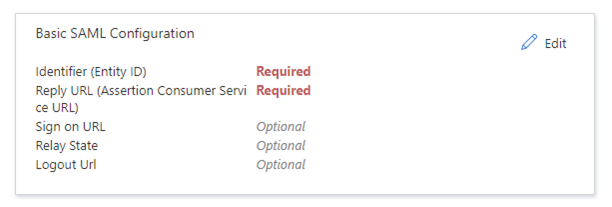
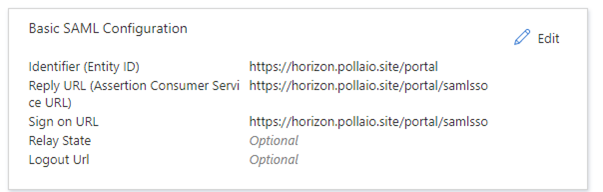
Insert:
Identifier -> https://<public-FQDN-UAG>/portal
Reply URL -> https://<public-FQDN-UAG>/portal/samlsso
Sign on URL -> https://<public-FQDN-UAG>/portal/samlsso
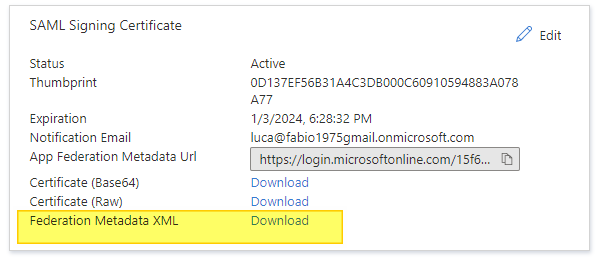
Download the XML
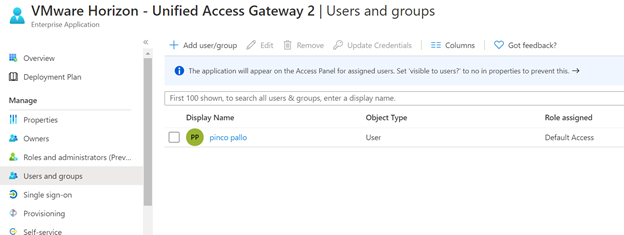
Assign Users or Groups permission to Enterprise application
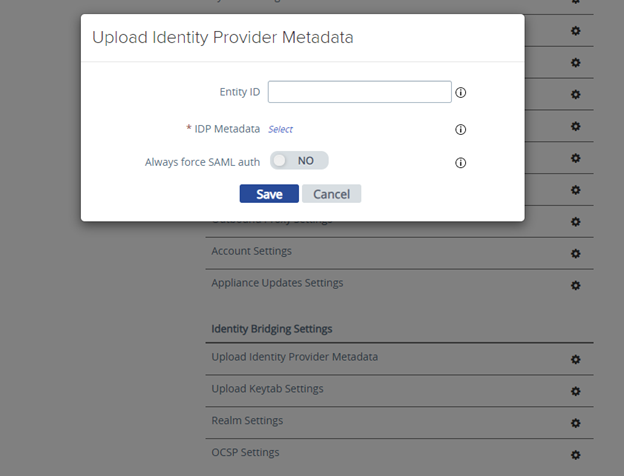
Import XML on UAG and configure it
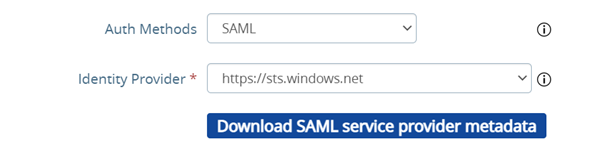
Import Identity Provider Metadata, select the file XML downloaded from the Enterprise Application data
Select the identity provider
Select More Option
And select SAML e the correct Identity provider (with SAML+PASSTROUGHT the identity token will not passed to horizon Server and it will required a new autentication)