When we need to integrate a Horizon infrastructure to the cloud identity provider (like Workspace One Access SaaS solution) sometimes we need to manage firewall and proxy configuration.
For the Firewall rule, there is much information (KB link) while for the proxy server, we are not able to use Windows server configuration because Horizon ignores it.
To use a proxy server to permit communication to the IdP URL from Horizon Connection servers we need to configure some values on ADAM DB:
pae-SAMLProxyName
pae-SAMLProxyPort
To connect to ADAM DB and where modify the correct value
- Connect with RDP session to Connection Server OS
- Start from PowerShell adsedit
- In the console tree select Connect to..
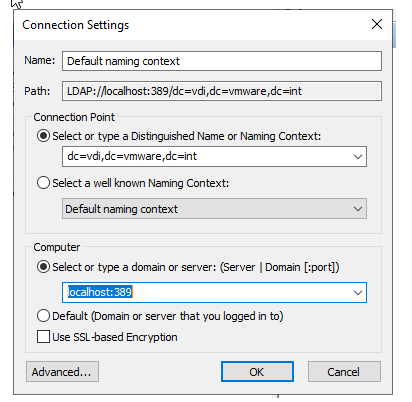
- Configure the connection with this information.
dc=vdi,dc=vmware,dc=int
localhost:389
- Expand ADAM ADSI tree under the object path: dc=vdi,dc=vmware,dc=int,ou=Properties,ou=Global
- Click on value Common and modify the following value
pae-SAMLProxyName -> With Proxy URL
pae-SAMLProxyPort -> With Proxy Port
Now we can configure the SAML integration from Horizon and IdP
Some information about why we need to integrate and use Workspace One Access with Horizon:
Integration between VMware Horizon and VMware Workspace ONE Access (formerly called Workspace ONE) uses the SAML 2.0 standard to establish mutual trust, which is essential for single sign-on (SSO) functionality. When SSO is enabled, users who log in to VMware Workspace ONE Access or Workspace ONE with Active Directory credentials can launch remote desktops and applications without having to go through a second login procedure.